Be aware that even though Donald Trump is getting all the polls going his way, in the end its Voting Machines that tally the votes and its the "Electoral College votes" that count and the Democrats control the VOTING AND COUNTING in most Key swing STATES where Republicans MUST win.
UNDERSTAND THAT the Dems start with an almost guaranteed 217 out of 270 for a win Electoral College votes. The states that are supposed to win it for the Republicans like Ohio, Pennsylvania and Florida have electronic voting and George Sorros and the Democrat operatives control that vote!
A little bit of information to share. Joseph Stalin said it best a long time ago. It does not matter who votes, it matters who counts those votes!
Question: Are Our National Elections Rigged? Answer: HELL YES FROM A LONG TIME AGO...
My warning to Donald Trump. Do not sit on the happy poll numbers. Its Voting Machines and the Electoral College that will vote for a president based on the vote count in specific states and right now its winner take all in every State.
Well of course they are. That's a foregone conclusion; not even a fit subject for intelligent debate any more. Oh, it's a little more sophisticated now than in the days of the old Tennessee custom of a Mason jar of moonshine, or the Chicago precinct captain's distribution of "walking around money." But the practice is alive and well, and more pervasive than ever. The evidence is everywhere if we choose to look.
Of course, there is a pattern here that favors one political party over the other, but these are rather insignificant isolated instances compared to the big picture that is beginning to emerge. I believe it was Joseph Stalin who said, "It's not the people who vote that counts. It's the people who count the votes." That advice has been taken to heart by our current crop of politicians.
Is political tampering new? Of course not. In 1915 mass indictments for voter fraud were handed down in Terre Haute, IN, in which the incumbent sheriff, and the local judge, and the Terre Haute mayor were all sentenced to the pokey. By 1932 Louisiana senator Huey "Kingfish" Long had polished the process to the point that he won unanimously in sixteen New Orleans precincts and tallied identical votes in 28 others. New York's Tammany Hall political machine bought off judges, politicians, ward captains, and controlled Democrat Party nominations for more than a century. What is new is the size and scope of election tampering now made possible with current electronic monitoring and tabulation.
Mass corruption began in earnest in 2002 with the passage of another of those laws with the cutsie little name of the "Help Americans Vote Act," which gave states $3.9 BILLION if they would to do away with balloting that left a paper trail, and substituted what was termed "Direct Recording Electronic" (DRE) voting machines. This took vote counting away from local communities and transferred it to centralized voting centers with political interests in the outcome. (Please remember the aforementioned Joseph Stalin quotation.)
A number of hardware manufacturers got into the act with no electronic experience, but lots of political connections. None worse than Diebold, a producer of wall safes. Their voting machine subsidiary was so dysfunctional that its collection of ballots was easily hacked, remotely or on-site, using any off-the-shelf version of the Microsoft "Access" program. The US Department of Energy's Argonne National Laboratory issued a report that the outcome of an entire election could be arranged by anyone with $26 in parts and an 8th grade science education. Diebold's reputation was so bad that they eventually changed their name to "Premier Election Solutions." But by then the damage was done, so Diebold got out of the election business altogether, selling out to "Election Systems and Software" (ES&S).
This story has so many ins-and-outs, and involves too many interconnecting politicians and entities, I will follow only one. The aforementioned Election Systems and Software (ES&S).
The date: 1996. The location: Nebraska. The event: A senate race. From out of nowhere, a virtually unknown millionaire named Chuck Hagel staged an amazing upset victory over the popular Democrat Governor Ben Nelson, who had been elected in a landslide only two years previously. It was little known at the time, but two weeks before announcing his candidacy, Chuck Hagel had stepped down as CEO of ES&S, the firm that would soon count his own senate votes. He won, of course.
In 2002 Hagel was challenged by Democrat Charlie Natulka. The votes were again electronically tabulated by ES&S, and this time Hagel won 83% of the vote, the largest margin of victory ever recorded in Nebraska history!
Matulka's request for an investigation by the Senate Ethics Committee was denied. Would not have mattered though since Nebraska law states that recounts must be conducted using the same "vote-counting device" used in the actual election, which, of course, would be the same ES&S machine.
There are many, many, other facets to this voter corruption scandal. I have only scratched the surface with this one, and I am already running out of space, but let me conclude this one part by asking that you please keep in mind that this is the same Chuck Hagel, who after serving two terms in the United States Senate, is now the Obama administration's recently appointed Secretary of Defense.
Who says that crime doesn't pay? Depends on the game, I guess.
When George Sorros and the Obama Cabal took over the Voting Machine ownership and used it for their own wins, they blackmailed Chuck Hagel into silence and then offered a position in their cabal. He accepted the offer he could not refuse!
Still doubting that our elections are rigged, you can view the video below and hear first-hand the sworn testimony of a Mr. Clinton Eugene Curtiss before a select United States Senate Committee, admitting that he was retained by former Florida Congressman Tom Feeney, then Speaker of the Florida House of Representatives, to develop a program for the specific purpose of determining the outcome of electronically tabulated elections.
This, and other election-throwing computer programs, became vital to the outcome of the 2012 presidential election. Voters in Ohio, Pennsylvania, Nevada, North Carolina, and Texas all reported that a vote for Romney resulted in either a direct or a default vote for Obama. The Market Daily News reported that in 100 Cuyahoga County (Cleveland) Ohio precincts, Obama got 99% of the votes and Romney 0. In more than 50 different precincts, Romney received two votes or less. In Philadelphia, 59 precincts recorded not one single vote for Romney. And the list goes on. How is this possible? I will attempt to answer this question as you again remember the Joseph Stalin quotation, "It's not the people who vote that counts. It's the people who count the votes."
In 2002, the use of "Direct Recording Electronic" (DRE) voting machines and the elimination of all paper trails of balloting was imposed upon the states through the enactment of the "Help Americans Vote Act." Since the conduct of elections is constitutionally delegated to the sovereign states, the feds came up with a $3.9 BILLION inducement for them to adopt electronic voting. Obviously, there was a lot of money and a lot of political influence involved in concentrating the tabulation of balloting into the hands of a select few. A few with connections in high places.
How could so many similar events be occurring simultaneously in so many different locations? READ ON...
Enter now from left stage, the Urosevich brothers, Bob and Ted. They respectively controlled Ohio-based Diebold and its theatrical stand-in, Nebraska-based "Election Systems and Software" (ES&S). Diebold eventually sold out to ES&S, thus ending the competition charade. There then emerged another major performer in this off-Broadway production --- Sequoia. Its machines serviced nearly 9 million voters in the 2012 election.
The Diebold-ES&S collaboration was temporarily disrupted by a Justice Department ant-trust indictment, forcing ES&S to sell its Diebold interest to the Dominion Corporation --- the fourth largest name in voter technology. But a month later, the DOJ turned a blind eye as Dominion purchased Sequoia. So now, the cast of players was complete. Only two domestic voting machine manufacturers remained on stage -- ES&S and Dominion.
About that time, things got a little dicey in the head offices. Many of the key staffers were accused or convicted of a dizzying array of white-collar crimes, including conspiracy, bribery, bid rigging, computer fraud, tax fraud, stock fraud, mail fraud, extortion, and drug trafficking.
While their interests were directed elsewhere, newer technologies, including Web-based voting, emerged on the scene in the form of the Spanish-owned firm, Scytl. And to keep things nice and cozy, Scytl named our old friend Bob Urosevich, of Diebold fame, as managing director of its Americas division.
Scytl became the subject of much speculation that the tabulation of domestic balloting had been outsourced by the Obama administration to this Spanish firm, owned by international financier, George Soros. True, Scytl had been contracted to handle some overseas military ballots, but there is apparently no basis to the Obama outsourcing story, or ownership by George Soros. However, Scytl is believed to have provided the Web-based technology to Allpoint Voter Services, used by the North Carolina State Board of Elections and the Obama campaign's GottaRegister.com website to enroll at least 11,000 persons via the internet, in violation of North Carolina state law.
So, as the curtain falls on what has now become an American Tragedy in voting, the very foundation of our Representative Republic, the right to free and open elections, is now concentrated in the hands of a few politically connected entities; entities that are neither free nor open. WE MUST BE AWARE OF THIS EARLY AND DONALD TRUMP MUST PREPARE HIS BATTLE PLANS TO FIGHT NOW AND NOT LATER!
Tampering of elections has progressed from the outmoded inefficiency of buying a single vote through the offering of a Mason jar of bootleg whiskey or the dispensing of a little "walking around money," to the current practice of influencing entire elections. Why? Because, as Joseph Stalin so accurately observed many years ago, "It's not the people who vote that counts. It's the people who count the votes."
Act II showed how control of the entire voting process became possible through the outlawing of the paper ballot, and its inconvenient trail of truth, and replacing it with the Direct Recording Electronic (DRE) voting machine -- capable of manipulating the votes of many, in order to benefit the few.
Act III now opens to show that sinister plots were already at play in the presidential election of 2012, even before the ballots were cast. Return with us now to those golden days of yesteryear; to the mystical, magical land of Camelot; to the days of the Kennedy administration; to the enactment of the National Voter Registration Act of 1993, also known as the Motor Voter Act. This legislation requires states to accept voter-registration applications for federal (i.e., House, Senate, and Presidential) elections by three principal means:
- By being registered to vote if applying for, or renewing, a driver's license (hence the name “motor voter”)
- By being registered to vote upon application at all offices that provide public assistance of any kind -- including Obamacare -- thus appealing to those who are receiving free or subsidized assistance to favor the party in power.
- By voter-registration applications being accepted on line, or by mail, with no verification of legitimacy.
- Some eight million people have registered this way, but only about five percent of them usually bother to vote -- leaving a considerable pool of names available to those bent on election mischief.
- Only seven states require photo IDs at polling booths -- making it easier to vote in someone else's name, either in person or by absentee ballot. Last July 18th, Senate Bill S.1336 was submitted by Senator Ted Cruz (R-TX), et al., to amend the National Voter Registration Act of 1993 to permit all States to require proof of citizenship for registration to vote in elections for Federal office. However, Senate Leader Harry Reid (D-NV) has not brought the bill up for consideration.
- Motor Voter made it illegal to check the IDs of applicants.
In July 2010, a newly-formed voter registration group, Houston Votes, investigated a sampling of registered voters, and brought their results to the local paper, the Harris County Registrar. Of 25,640 new registration applications submitted, only 7,193 were actually new voters, the remainder being a deliberate effort to over-burden the processing system with thousands of duplicate and incomplete voter registration applications, in keeping with the Cloward-Piven strategy of governmental overthrow by clogging legitimate government function with overwhelming public demands.
So how is all this possible? Easy. As an example, a call to the State Department of Transportation (DOT) driver's license bureau revealed that although they do require an applicant to submit a Social Security number (SS#), and although the DOT does have access to a Federal database for SS# verification, they seldom do so since the legitimacy of a valid SS# is not of concern to the issuer of drivers' licenses.
If the applicant indicates a willingness to be registered to vote, which the wording of the form encourages the applicant to do, a copy of the applicant's personal information is transmitted directly to the appropriate county Election Commission Office, where the application is processed, and a voter registration card issued.
However, although a valid SS# is required for voter registration, the Election Commission Office has no means of checking its authenticity, but assumes the information provided was verified by the originating government agency.
So the government agency with the capacity to verify the citizen's ID, often doesn't; and the government agency with the need to verify the citizen's ID, can't. The loophole is obvious. This is one reason why the Motor Voter Act, the brainchild of the same NYC Columbia University professors Richard Cloward and Frances Fox Piven mentioned previously, has been termed the nation's primary source of voter irregularities; and it's all perfectly legal.
So there you have it. Is this going to be the final act? I would like to think that we might have a happy ending, but if so, we had better get to work on it. Time is running out, and the final curtain on legitimate elections is fast closing.
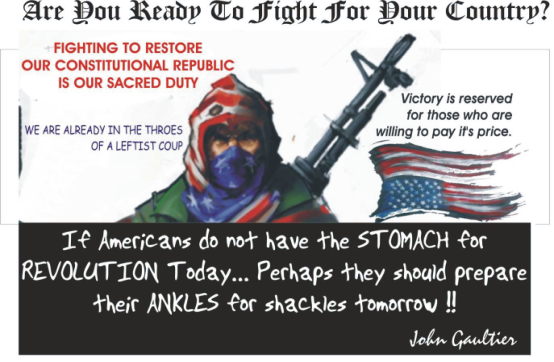
So what's the answer? Short of an armed revolution that none of you all in large numbers are willing to join and I have called for for over 7 years, it can only be found at the ballot box, corrupt though it may be.
Our voting for Donald Trump in the elections of 2016 must be so overwhelming that they defy those who would corrupt the outcome. Will it be easy? Certainly not. Can we do it HELL YES.. we must.
THE SILENT CONSERVATIVE MAJORITY MUST GET OFF THEIR ASSES AND MOBILIZE NOW.
Plan to have observers and counters at polling places with a dubious past and track the votes. We must also demand that in the case of outright fraud, this time the Republican Party will stand up and fight and not cower in fear like they did in 2012!
EXPOSED! Hagel and Obama use the same voting machines to Win their elections!
SOCIALISTS MAKE LONG TERM PLANS!!:Obama wins Ohio and PA with margins that boggle the mind. ( 100% in some precincts!)Well...Guess who was in charge of the company that makes the machines that count the votes??? The longer we allow them to use these machines the worse it becomes for the chances for Conservatives to win anywhere there are electronic voting machines.CHUCK HAGEL: Now he is getting his payback. So he too can cash in on the Cash Cow that is the federal Government. Look you think these guys make their money from the paycheck they get ?? HELL NO!! Its the Kickbacks and secret deals with bank accounts in Arab Countries outside the reach of the IRS. Same reason Al Gore went with Al Jazeera. Obama and got a secret kick back in QATAR or Dubai or some other Arab country. Back to Hagel: In 1992, Hagel was CEO of Election Systems & Software, maker of computerized voting machines.
On March 15, 1995, Hagel resigned as CEO but kept millions in stock options and declared that he was going to run for the U.S. Senate in Nebraska. Although he was a virtually unknown candidate; although he ran against a former governor, Ben Nelson, who was hugely popular; and although all the polls prior to the election indicated Ben Nelson would win the election, oddly Hagel won by a landslide with 83% of the vote.
It later turned out that Hagel’s voting machines had been used in virtually all of the precincts.
When Hagel ran for reelection in 2006, his previous landslide of 83% was eclipsed by an even wider margin.
It turns out that Hagel’s former company, Election Systems & Software/Diebold now counts the votes in most elections. Who has controlling interest in it now ? The Omaha Group with the secret backing of Warren Buffet and the other vote counting machine company is owned in some way by George Soros.
And it turns out Hagel’s voting machines have been embroiled in investigations of hacking and vote-switching that continue to this day.
Now consider this....Barack Obama won the presidential elections the same way Hagel won his senatorial seat? How? By using those machines to defraud the electorate and he was given the position of Secretary of Defense as a kick back for the favor?
Americans should demand to see each and every vote cast for both Chuck Hagel and Barack Obama.
Now. Today, WE ARE BEING DUPED PATRIOTS... TIME FOR A REVOLUTION !!! BEFORE IT IS TOO LATE!
FYI: Diebold voting machines can be hacked by remote control
It could be one of the most disturbing e-voting machine hacks to date.
Voting machines used by as many as a quarter of American voters heading to the polls in 2012 can be hacked with just $10.50 in parts and an 8th grade science education, according to computer science and security experts at the Vulnerability Assessment Team at Argonne National Laboratory in Illinois. The experts say the newly developed hack could change voting results while leaving absolutely no trace of the manipulation behind.
“We believe these man-in-the-middle attacks are potentially possible on a wide variety of electronic voting machines,” said Roger Johnston, leader of the assessment team “We think we can do similar things on pretty much every electronic voting machine.”
The Argonne Lab, run by the Department of Energy, has the mission of conducting scientific research to meet national needs. The Diebold Accuvote voting system used in the study was loaned to the lab’s scientists by VelvetRevolution.us, of which the Brad Blog is a co-founder. Velvet Revolution received the machine from a former Diebold contractor.
Previous lab demonstrations of e-voting system hacks, such as Princeton’s demonstration of a viral cyber attack on a Diebold touch-screen system relied on cyber attacks to change the results of elections. Such attacks, according to the team at Argonne, require more coding skills and knowledge of the voting system software than is needed for the attack on the Diebold system.
Indeed, the Argonne team’s attack required no modification, reprogramming, or even knowledge, of the voting machine’s proprietary source code. It was carried out by inserting a piece of inexpensive “alien electronics” into the machine.
The Argonne team’s demonstration of the attack on a Diebold Accuvote machine is seen in a short new video shared exclusively with the Brad Blog [posted below]. The team successfully demonstrated a similar attack on a touch-screen system made by Sequoia Voting Systems in 2009.
The new findings of the Vulnerability Assessment Team echo long-ignored concerns about e-voting vulnerabilities issued by other computer scientists and security experts, the U.S. Computer Emergency Readiness Team (an arm of the Department of Homeland Security), and even a long-ignored presentation by a CIA official given to the U.S. Election Assistance Commission.
“This is a national security issue,” says Johnston. “It should really be handled by the Department of Homeland Security.”
The use of touch-screen Direct Recording Electronic (DRE) voting systems of the type Argonne demonstrated to be vulnerable to manipulation has declined in recent years due to security concerns, and the high cost of programming and maintenance. Nonetheless, the same type of DRE systems, or ones very similar, will once again be used by a significant part of the electorate on Election Day in 2012.
According to Sean Flaherty, a policy analyst for VerifiedVoting.org, a nonpartisan e-voting watchdog group, “About one-third of registered voters live where the only way to vote on Election Day is to use a DRE.”
Almost all voters in states like Georgia, Maryland, Utah and Nevada, and the majority of voters in New Jersey, Pennsylvania, Indiana and Texas, will vote on DREs on Election Day in 2016, says Flaherty. Voters in major municipalities such as Houston, Atlanta, Chicago and Pittsburgh will also line up in next year’s election to use DREs of the type hacked by the Argonne National Lab.
Voting machine companies and election officials have long sought to protect source code and the memory cards that store ballot programming and election results for each machine as a way to guard against potential outside manipulation of election results. But critics like California Secretary of State Debra Bowen have pointed out that attempts at “security by obscurity” largely ignore the most immediate threat, which comes from election insiders who have regular access to the e-voting systems, as well as those who may gain physical access to machines that were not designed with security safeguards in mind.
“This is a fundamentally very powerful attack and we believe that voting officials should become aware of this and stop focusing strictly on cyber [attacks],” says Vulnerability Assessment Team member John Warner. “There’s a very large physical protection component of the voting machine that needs to be addressed.”
The team’s video demonstrates how inserting the inexpensive electronic device into the voting machine can offer a “bad guy” virtually complete control over the machine. A cheap remote control unit can enable access to the voting machine from up to half a mile away.
“The cost of the attack that you’re going to see was $10.50 in retail quantities,” explains Warner in the video. “If you want to use the RF [radio frequency] remote control to stop and start the attacks, that’s another $15. So the total cost would be $26.”
The video shows three different types of attack, each demonstrating how the intrusion developed by the team allows them to take complete control of the Diebold touch-screen voting machine. They were able to demonstrate a similar attack on a DRE system made by Sequoia Voting Systems as well.
In what Warner describes as “probably the most relevant attack for vote tampering,” the intruder would allow the voter to make his or her selections. But when the voter actually attempts to push the Vote Now button, which records the voter’s final selections to the system’s memory card, he says, “we will simply intercept that attempt … change a few of the votes,” and the changed votes would then be registered in the machine.
“In order to do this,” Warner explains, “we blank the screen temporarily so that the voter doesn’t see that there’s some revoting going on prior to the final registration of the votes.”
This type of attack is particularly troubling because the manipulation would occur after the voter has approved as “correct” the on-screen summaries of his or her intended selections. Team leader Johnson says that while such an attack could be mounted on Election Day, there would be “a high probability of being detected.” But he explained that the machines could also be tampered with during so-called voting machine “sleepovers” when e-voting systems are kept by poll workers at their houses, often days and weeks prior to the election or at other times when the systems are unguarded.
“The more realistic way to insert these alien electronics is to do it while the voting machines are waiting in the polling place a week or two prior to the election,” Johnston said. “Often the polling places are in elementary schools or a church basement or some place that doesn’t really have a great deal of security. Or the voting machines can be tampered while they’re in transit to the polling place. Or while they’re in storage in the warehouse between elections,” says Johnston. He notes that the Argonne team had no owner’s manual or circuit diagrams for either the Diebold or Sequoia voting systems they were able to access in these attacks.
The team members are critical of election security procedures, which rarely, if ever, include physical inspection of the machines, especially their internal electronics. Even if such inspections were carried out, however, the Argonne scientists say the type of attack they’ve developed leaves behind no physical or programming evidence, if properly executed.
“The really nice thing about this attack, the man-in-the-middle, is that there’s no soldering or destruction of the circuit board of any kind,” Warner says. “You can remove this attack and leave no forensic evidence that we’ve been there.”
Gaining access to the inside of the Diebold touch-screen is as simple as picking the rudimentary lock, or using a standard hotel minibar key, as all of the machines use the same easily copied key, available at most office supply stores.
“I think our main message is, let’s not get overly transfixed on the cyber,” team leader Johnston says. Since he believes they “can do similar things on pretty much every electronic voting machine,” he recommends a number of improvements for future e-voting systems.
“The machines themselves need to be designed better, with the idea that people may be trying to get into them,” he says. ” If you’re just thinking about the fact that someone can try to get in, you can design the seals better, for example.”
“Don’t do things like use a standard blank key for every machine,” he warns. “Spend an extra four bucks and get a better lock. You don’t have to have state of the art security, but you can do some things where it takes at least a little bit of skill to get in.”
So i am warning the Conservatives and the Trump Team.
Do not sit on the happy poll numbers. Its Voting Machines and the Electoral College that will vote for a president based on the vote count in specific states and right now its winner take all in every State.
So if the playing field is level Trump will win. If he does.... My Advise to his new Administration.
Do not rest on the laurels of victory. Use the 4 years you will have in office to make it a mission to remove the Electronic Voting Machines from the counting of votes in Federal elections. You cannot change how States vote but you can for Federal Selections. If you don't I fear that the cheating using electronic voting machines will become worse and worse with every election cycle and the Democrats and the Obama backers will perfect "THE ART OF THE CHEATING" and elections will always be won by the Socialist Democrats gunning to steal our country. its their long game as I said.




No comments:
Post a Comment